Technical Account Module - Technical Assets
Overview
The 'Technical Asset' extends CzechIdM's technical account module capabilities by introducing a new entity type that groups and manages technical accounts. This module enables organizations to associate technical accounts with specific assets, assign guarantors and holders through both direct assignment and role-based mechanisms, and implement comprehensive audit trails for all operations.
Purpose
Centralize management of technical accounts under logical asset groupings
Enable role-based access control for asset-related operations
Provide audit capabilities for compliance requirements
Support notifications via NOTIFY event
Entities
ER Diagram
┌──────────────────┐ ┌────────────────┐
│ TechnicalAccount │◄─ ─ ─│ TechnicalAsset │
└──────────────────┘ └────────────────┘
│
│ ┌─────────────────────────┐
├─────►│ TechnicalAssetGuarantor │◄────────┐
│ └─────────────────────────┘ │ ┌─────────────┐
│ ├─────│ IdmIdentity │
│ ┌──────────────────────┐ │ └─────────────┘
├─────►│ TechnicalAssetHolder │◄───────────┘
│ └──────────────────────┘
│
│ ┌─────────────────────────────┐
├─────►│ TechnicalAssetGuarantorRole │◄────┐
│ └─────────────────────────────┘ │ ┌─────────┐
│ ├─────│ IdmRole │
│ ┌──────────────────────────┐ │ └─────────┘
└─────►│ TechnicalAssetHolderRole │◄───────┘
└──────────────────────────┘
TechnicalAccount
The technical account has been extended with an optional attribute specifying which technical asset it belongs to.
Key Attributes
| Attribute | Type | Description |
| technicalAsset | UUID | optional attribute specifying which technical asset the technical account belongs to |
Evaluators
| Evaluator | Type | Description | Attributes |
| TechnicalAccountByTechnicalAssetGuarantorEvaluator | Regular | Returns technical accounts where the logged user is a guarantor of the parent technical asset - either directly by identity or indirectly by role. Technical accounts without an assigned technical asset are never matched by this evaluator. | No attributes |
| TechnicalAccountByTechnicalAssetHolderEvaluator | Regular | Returns technical accounts where the logged user is a holder of the parent technical asset - either directly by identity or indirectly by role. Technical accounts without an assigned technical asset are never matched by this evaluator. | No attributes |
| TechnicalAccountByTechnicalAssetTransitiveEvaluator | Transitive | Returns technical accounts where the logged user has access to the parent technical asset. Permissions are transitively derived from the technical asset the technical account belongs to. Technical accounts without an assigned technical asset are never matched by this evaluator. | Transfer permissions - a list of permissions to be transferred from a technical asset to its technical accounts; if the list is empty, all permissions held by the user for the given technical asset will be transferred to its technical accounts |
TechnicalAsset
The primary entity representing a technical asset that can contain multiple technical accounts.
Key Attributes
| Attribute | Type | Description |
| id | UUID | primary identifier |
| name | String | asset name |
| description | String | asset description |
| disabled | Boolean | flag indicating whether the asset is disabled |
| externalId | String | identifier assigned by an external system for integration purposes |
| externalCode | String | code from an external system |
| validFrom | LocalDate | validity start date |
| validTill | LocalDate | validity end date |
Permissions
| Permission | Description |
| ADMIN | all permissions |
| COUNT | permission to retrieve the count of entities |
| AUTOCOMPLETE | permission to display the entity in autocomplete suggestions |
| READ | permission to read the entity |
| CREATE | permission to create the entity |
| UPDATE | permission to edit entity attributes |
| DELETE | permission to delete the entity |
| SETTOTECHNICALACCOUNT | permission to assign a technical account to the given Technical Asset |
Evaluators
| Evaluator | Type | Description | Attributes |
| TechnicalAssetByGuarantorEvaluator | Regular | Returns technical assets where the logged user is a guarantor - either directly by identity or indirectly by role. | No attributes |
| TechnicalAssetByHolderEvaluator | Regular | Returns technical assets where the logged user is a holder - either directly by identity or indirectly by role. | No attributes |
TechnicalAssetGuarantor
Represents direct assignment of an identity as guarantor for a technical asset.
Key Attributes
| Attribute | Type | Description |
| id | UUID | primary identifier |
| externalId | String | identifier assigned by an external system for integration purposes |
| technicalAsset | UUID | id of the technical asset to be guaranted |
| guarantor | UUID | id of the user to be guarantor |
Permissions
| Permission | Description |
| ADMIN | all permissions |
| COUNT | permission to retrieve the count of entities |
| AUTOCOMPLETE | permission to display the entity in autocomplete suggestions |
| READ | permission to read the entity |
| CREATE | permission to create the entity |
| UPDATE | permission to edit entity attributes |
| DELETE | permission to delete the entity |
Evaluators
| Evaluator | Type | Description | Attributes |
| TechnicalAssetGuarantorByTechnicalAssetGuarantorEvaluator | Regular | Returns technical asset guarantors where the logged user is a guarantor of that technical asset - either directly by identity or indirectly by role. | No attributes |
| TechnicalAssetGuarantorByTechnicalAssetHolderEvaluator | Regular | Returns technical asset guarantors where the logged user is a holder of that technical asset - either directly by identity or indirectly by role. | No attributes |
| TechnicalAssetGuarantorByTechnicalAssetTransitiveEvaluator | Transitive | Returns technical asset guarantors where the logged user has access to the parent technical asset. Permissions are transitively derived from the technical asset the technical asset guarantor belongs to. | Transfer permissions - a list of permissions to be transferred from a technical asset to its guarantors; if the list is empty, all permissions held by the user for the given technical asset will be transferred to its guarantors |
TechnicalAssetGuarantorRole
Represents the assignment of a role to a technical asset, where granting this role to a user designates them as a guarantor of that asset
Key Attributes
| Attribute | Type | Description |
| id | UUID | primary identifier |
| externalId | String | identifier assigned by an external system for integration purposes |
| technicalAsset | UUID | id of the technical asset to be guaranted |
| role | UUID | id of the role which, when assigned to a user, makes them a guarantor |
Permissions
| Permission | Description |
| ADMIN | all permissions |
| COUNT | permission to retrieve the count of entities |
| AUTOCOMPLETE | permission to display the entity in autocomplete suggestions |
| READ | permission to read the entity |
| CREATE | permission to create the entity |
| UPDATE | permission to edit entity attributes |
| DELETE | permission to delete the entity |
Evaluators
| Evaluator | Type | Description | Attributes |
| TechnicalAssetGuarantorRoleByTechnicalAssetGuarantorEvaluator | Regular | Returns technical asset guarantor roles where the logged user is a guarantor of that technical asset - either directly by identity or indirectly by role. | No attributes |
| TechnicalAssetGuarantorRoleByTechnicalAssetHolderEvaluator | Regular | Returns technical asset guarantor roles where the logged user is a holder of that technical asset - either directly by identity or indirectly by role. | No attributes |
| TechnicalAssetGuarantorRoleByTechnicalAssetTransitiveEvaluator | Transitive | Returns technical asset guarantor roles where the logged user has access to the parent technical asset. Permissions are transitively derived from the technical asset the technical asset guarantor role belongs to. | Transfer permissions - a list of permissions to be transferred from a technical asset to its guarantor roles; if the list is empty, all permissions held by the user for the given technical asset will be transferred to its guarantor roles |
TechnicalAssetHolder
Represents direct assignment of an identity as holder for a technical asset.
Key Attributes
| Attribute | Type | Description |
| id | UUID | primary identifier |
| externalId | String | identifier assigned by an external system for integration purposes |
| technicalAsset | UUID | id of the technical asset to be managed |
| holder | UUID | id of the user to be holder |
Permissions
| Permission | Description |
| ADMIN | all permissions |
| COUNT | permission to retrieve the count of entities |
| AUTOCOMPLETE | permission to display the entity in autocomplete suggestions |
| READ | permission to read the entity |
| CREATE | permission to create the entity |
| UPDATE | permission to edit entity attributes |
| DELETE | permission to delete the entity |
Evaluators
| Evaluator | Type | Description | Attributes |
| TechnicalAssetHolderByTechnicalAssetGuarantorEvaluator | Regular | Returns technical asset holders where the logged user is a guarantor of that technical asset - either directly by identity or indirectly by role. | No attributes |
| TechnicalAssetHolderByTechnicalAssetHolderEvaluator | Regular | Returns technical asset holders where the logged user is a holder of that technical asset - either directly by identity or indirectly by role. | No attributes |
| TechnicalAssetHolderByTechnicalAssetTransitiveEvaluator | Transitive | Returns technical asset holders where the logged user has access to the parent technical asset. Permissions are transitively derived from the technical asset the technical asset holder belongs to. | Transfer permissions - a list of permissions to be transferred from a technical asset to its holders; if the list is empty, all permissions held by the user for the given technical asset will be transferred to its holders |
TechnicalAssetHolderRole
Represents the assignment of a role to a technical asset, where granting this role to a user designates them as a holder of that asset
Key Attributes
| Attribute | Type | Description |
| id | UUID | primary identifier |
| externalId | String | identifier assigned by an external system for integration purposes |
| technicalAsset | UUID | id of the technical asset to be guaranted |
| role | UUID | id of the role which, when assigned to a user, makes them a holder |
Permissions
| Permission | Description |
| ADMIN | all permissions |
| COUNT | permission to retrieve the count of entities |
| AUTOCOMPLETE | permission to display the entity in autocomplete suggestions |
| READ | permission to read the entity |
| CREATE | permission to create the entity |
| UPDATE | permission to edit entity attributes |
| DELETE | permission to delete the entity |
Evaluators
| Evaluator | Type | Description | Attributes |
| TechnicalAssetHolderRoleByTechnicalAssetGuarantorEvaluator | Regular | Returns technical asset holder roles where the logged user is a guarantor of that technical asset - either directly by identity or indirectly by role. | No attributes |
| TechnicalAssetHolderRoleByTechnicalAssetHolderEvaluator | Regular | Returns technical asset holder roles where the logged user is a holder of that technical asset - either directly by identity or indirectly by role. | No attributes |
| TechnicalAssetHolderRoleByTechnicalAssetTransitiveEvaluator | Transitive | Returns technical asset holder roles where the logged user has access to the parent technical asset. Permissions are transitively derived from the technical asset the technical asset holder role belongs to. | Transfer permissions - a list of permissions to be transferred from a technical asset to its holder roles; if the list is empty, all permissions held by the user for the given technical asset will be transferred to its holder roles |
Technical asset agenda
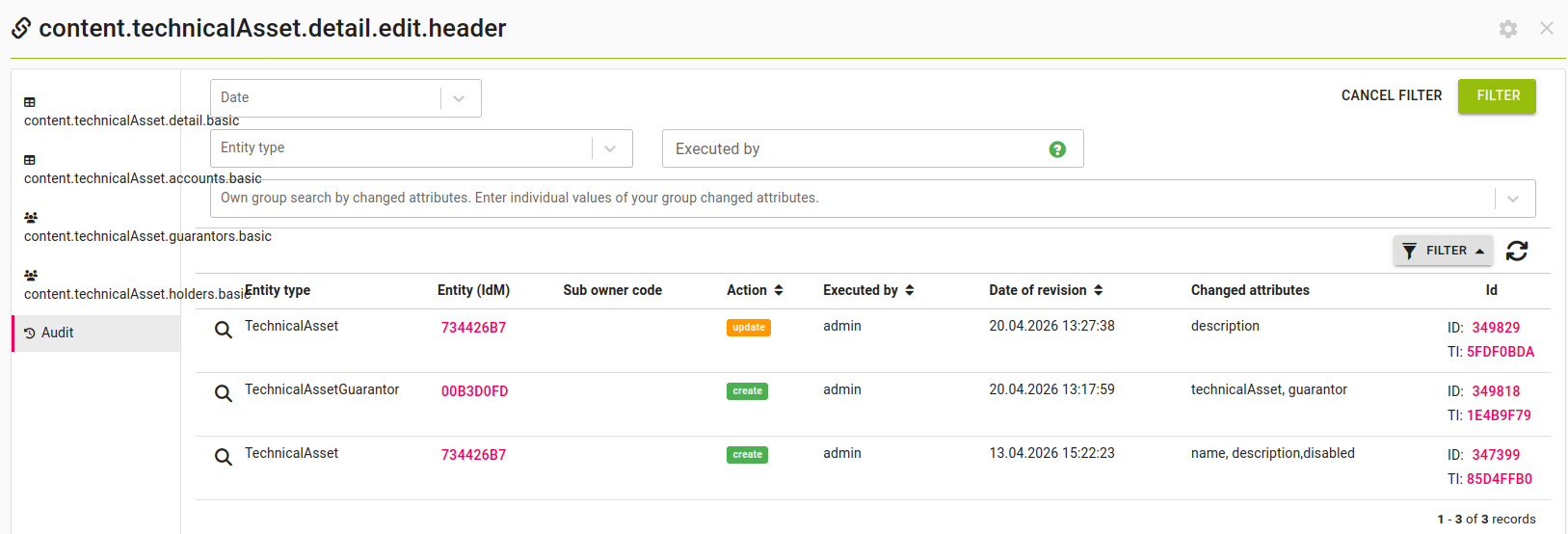
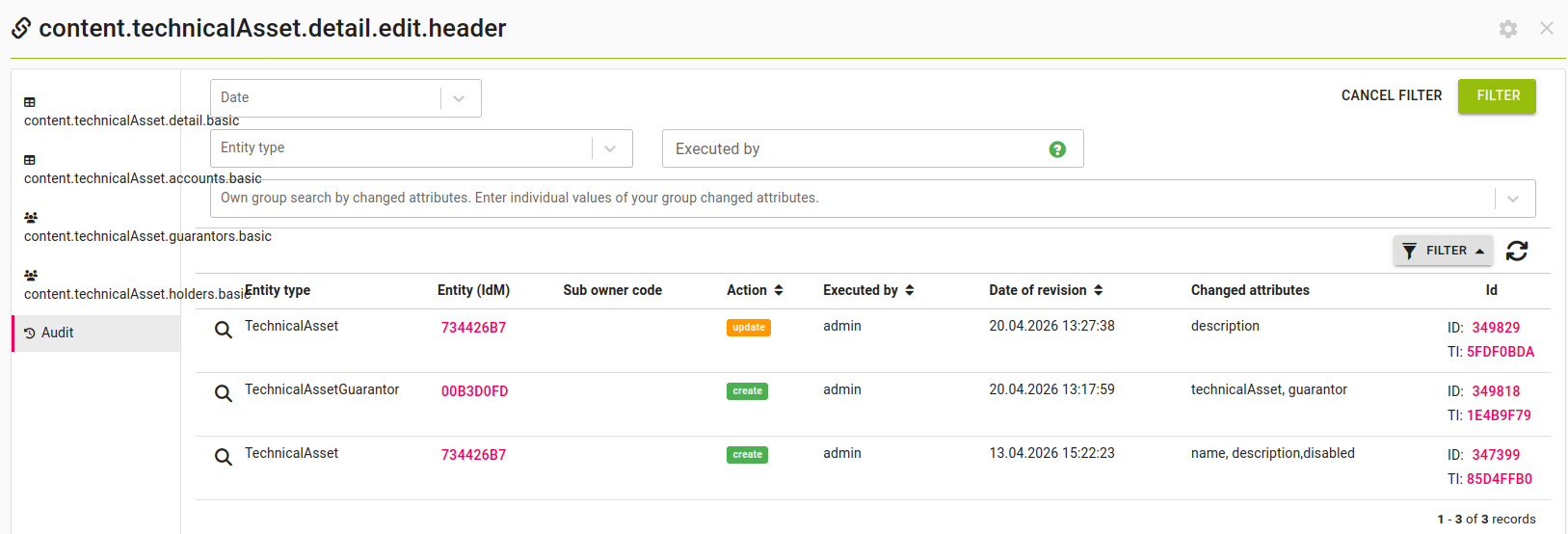
Technical asset audit
If you want to see the history of all operations with a given technical audit, you can use the Audit tab in its detail. In addition to changes to the entity itself (its name, description and disabled status) it also shows any additions/removals from the asset's assigned guarantors, holders and accounts.
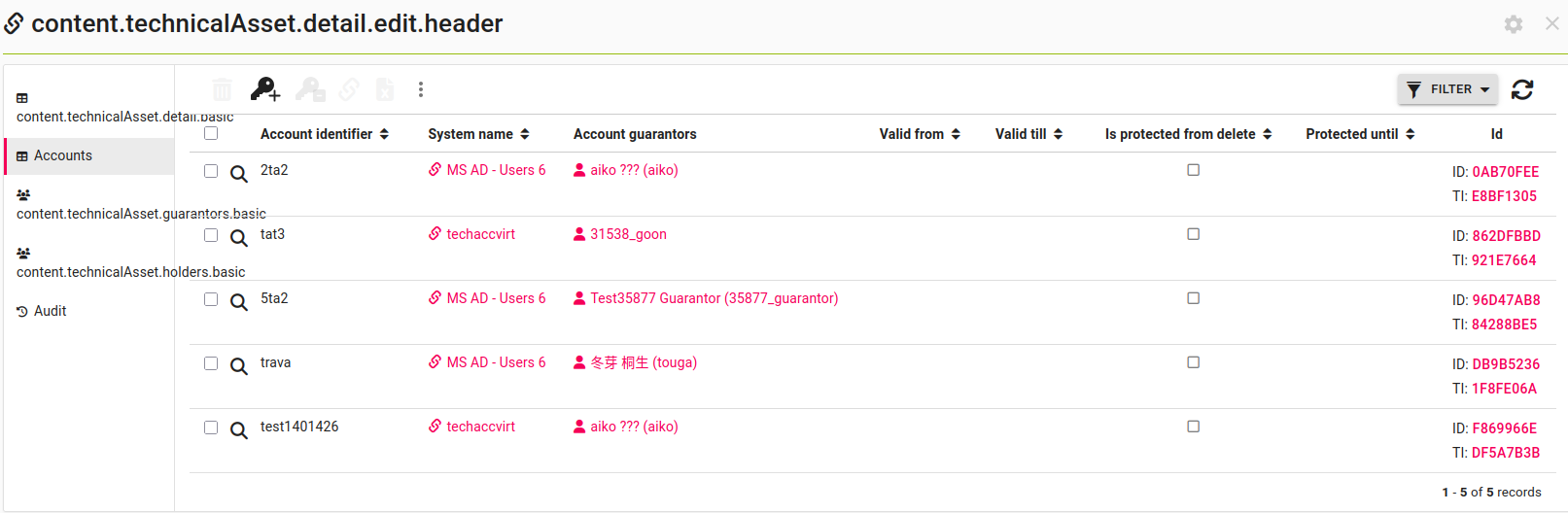
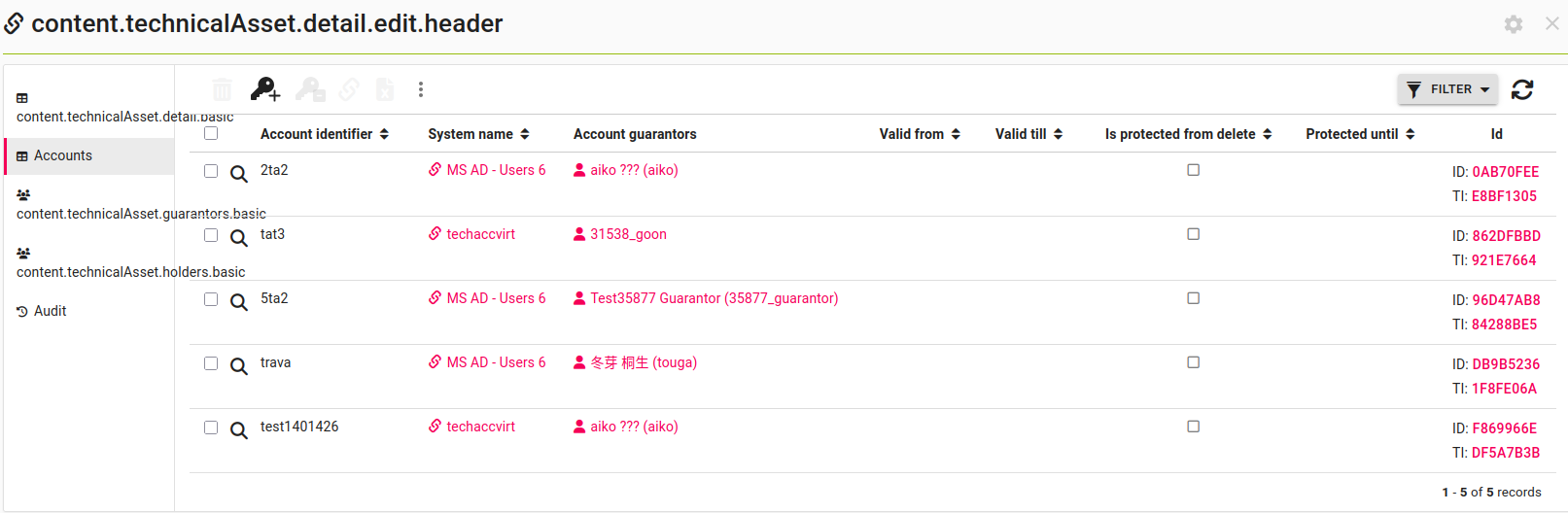
Technical asset accounts
If you want to see all the technical accounts that belong to a technical asset, you can use the Accounts tab of a technical asset detail. The table shown here has all the filtering features of the standard technical accounts table.