Table of Contents
Microsoft Active Directory (MS AD) wizard for groups
The main importance of wizards is to simplify the work of the user, so as to avoid complicated entering values and possibly to avoid common mistakes. System wizards are used primarily to create a new system connected to a given external system. The first step is to select the connector you want to use for the connection.
The most ambitious is the wizard for connecting the Microsoft Active Directory system (AD). Connecting AD within IdM is very important and at the same time manual connection can be a relatively complex matter for many and more advanced users. The complication starts in communication with AD. Here it is very important to use secure communication (SSL), which requires the installation of a correct certificate. It is also important to verify that our service AD account has sufficient privileges. However, the biggest difficulties can occur with many rules that must be followed during the connection (connector settings) and especially in the way to correctly map the individual attributes of AD. Selecting the correct attributes to map to AD may not be easy for inexperienced users.
More about synchronization of roles/groups you can find here.
This wizard therefore solves all the mentioned problems and is based on our best experience of how to effectively manage an AD system.
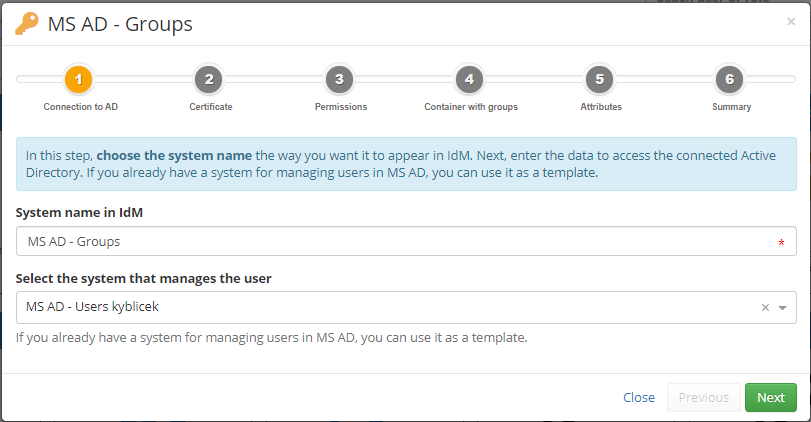
Connection to an AD system
In this step, choose the system name the way you want it to appear in IdM. Next, enter the data to access the connected Active Directory. If you already have a system for managing users in MS AD, you can use it as a template.
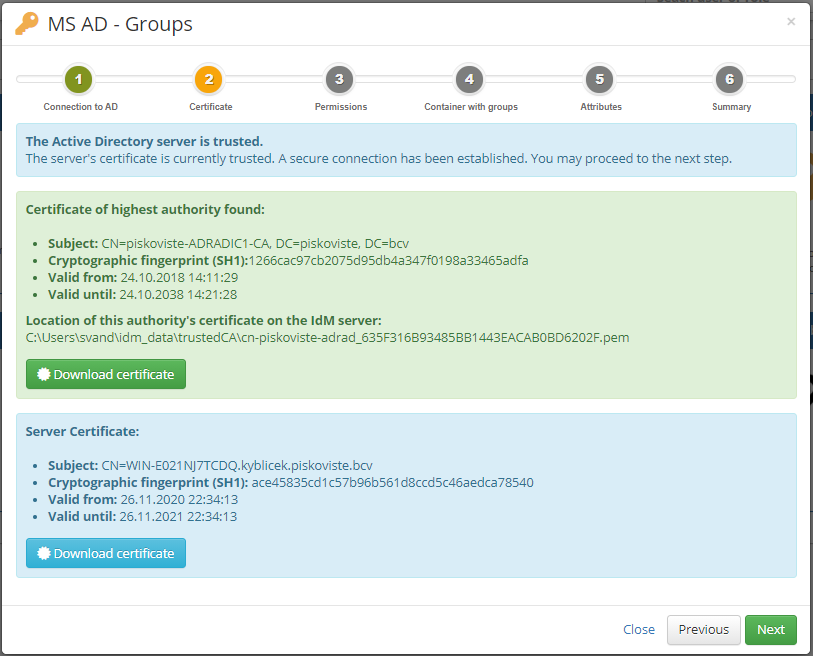
Certificate
In the second step, the wizard can download the certificate from the AD and save it to the server. First, the wizard verifies that your IdM server has the correct certificate installed for communication with AD. Next, the certificate is searched directly in AD. The goal is to find a certificate issued by the highest possible authority. The found certificate needs to be inserted into the trusted certificate store and the IdM restarted. The reason why we do not recommend using a server certificate directly in the trusted certificate store (it would be functionally sufficient) is its shorter validity (typically only 1 year).
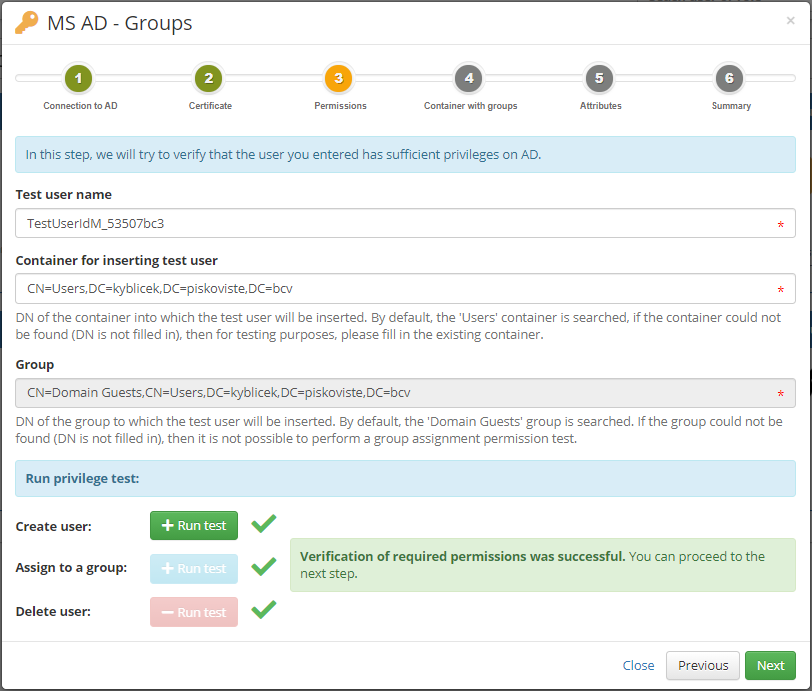
Check of permissions
In the next step, you have the option to perform a set of tests for a successful IdM connection. The most basic test is to create and delete a user. This will verify that you have correctly defined the rights for the service account that IdM accesses to AD and set the authentication information correctly in the previous steps.
Not all tests need to be performed to complete the connection. For example, grouping a user is an optional operation for some deployments
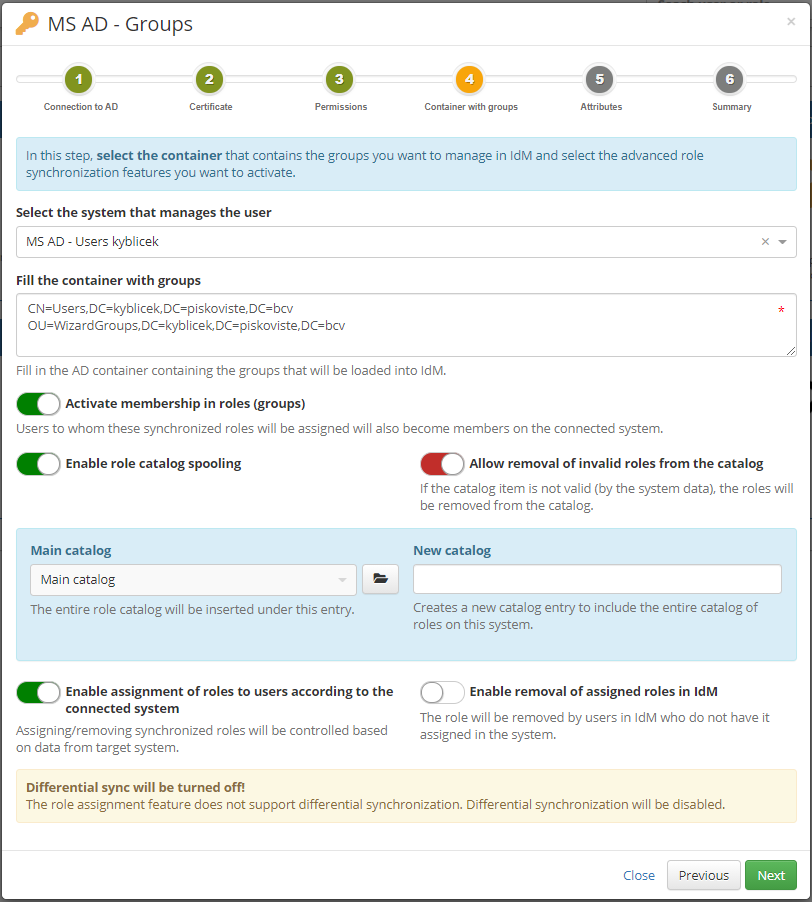
Additional data - containers with groups
The next step specifies in which OUs/containers groups are managed.
If you did not select a user management system mapping in MS AD in the first step, you must select one now.
Optional features:
- Membership in roles (groups) - The goal of membership management is to ensure that by assigning a role (created based on this synchronization) to a user, that role/group is provisioned to the end system with members.
- Role catalog management - Role catalog management ensures that synchronized roles are included in the IdM role catalog. How roles are cataloged depends on the transformation in the attribute that builds the catalog. In this wizard is choosed script for 'Put all role catalog items under main catalog from a sync' by default.
- Enable assignment of roles to users according to the connected system - This feature will ensure that we assign synchronized roles to existing users in IdM. In other words, the external system becomes the authority for IdM.
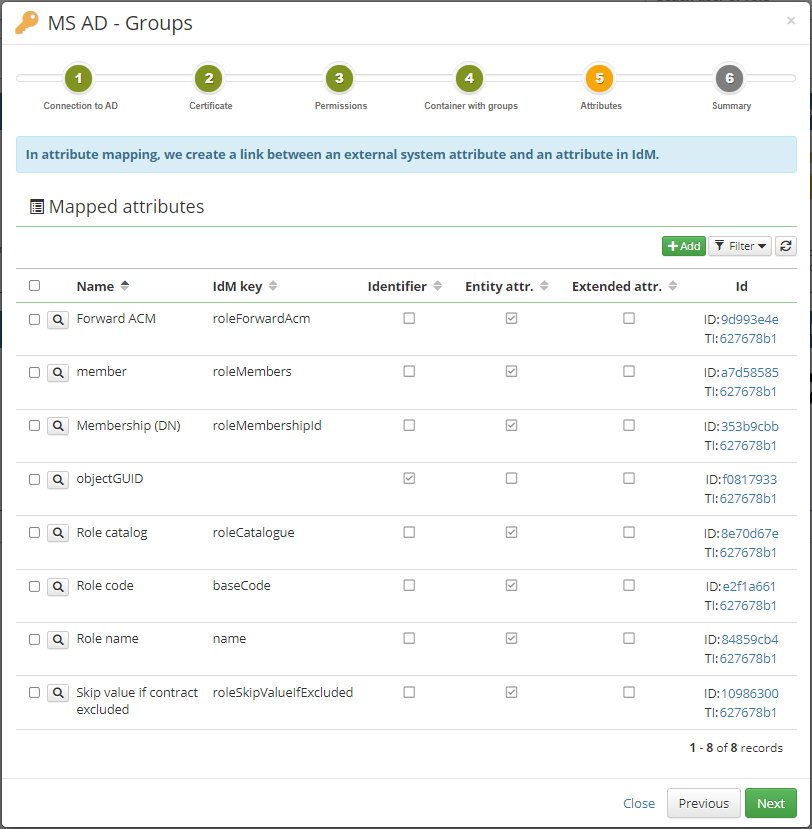
Attributes
In the penultimate step, the wizard prompts you to specify which attributes of the groups in AD you want to manage and from which role attribute in IdM you want to fulfill them.
The wizard automatically offers the most frequently used attributes and their typical fulfillment from CzechIdM. If there are some attributes that you do not use in your AD or do not want to fulfill, disable them or remove them from the list altogether.
By default, this wizard generates the following attribute mappings:
Basic role attributes in IdM:
- objectGUID - Primary identifier of the account in IdM.
- Role code - The role code in IdM uses the 'name' from the group in AD.
- Role name - The role name in IdM uses the 'name' from the group in AD.
Extra mapped attributes for advanced features:
- Membership (DN) - Resolves group memberships. Returns the role identifier (DN) that will be used in the role-system relation. The output value is String, if the value will be 'null', then the link between the role and the system will be removed!
- member - Returns a list of users to be assigned the role. The output is a list of identifiers from the system (typically DNs).
- Role catalog - Returns a list of role catalog nodes to which the role is to be assigned. If a more complex structure needs to be solved, then each node can contain (in embedded.parent) another catalog node.
- Forward ACM - Resolves group membership. Specifically manages the 'Forward provisioning' parameter.
- Skip value if contract excluded - Resolves group membership. Specifically, it manages the 'Skip value if contract is excluded' parameter.
Conclusion
The last step of this wizard only informs you about the successful completion and allows you to be redirected to the detail of the new system. For example, you can immediately start a sync of groups on this detail.