Modules - SCIM [scim]
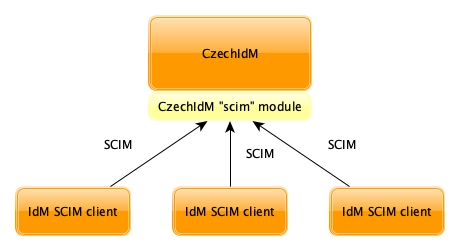
"scim" module exposes interface in CzechIdM by the SCIM 2.0 specification. Thus CzechIdM can be - as a server - connected to clients that implement SCIM 2.0 via its public API.
More about general SCIM specification - model, operations and endpoints.