Password provisioning
 Connectors that support changing a user's password (e.g., table, AD, LDAP, etc.) allow password provisioning. Each connector has specific settings for the password attribute.
Connectors that support changing a user's password (e.g., table, AD, LDAP, etc.) allow password provisioning. Each connector has specific settings for the password attribute.
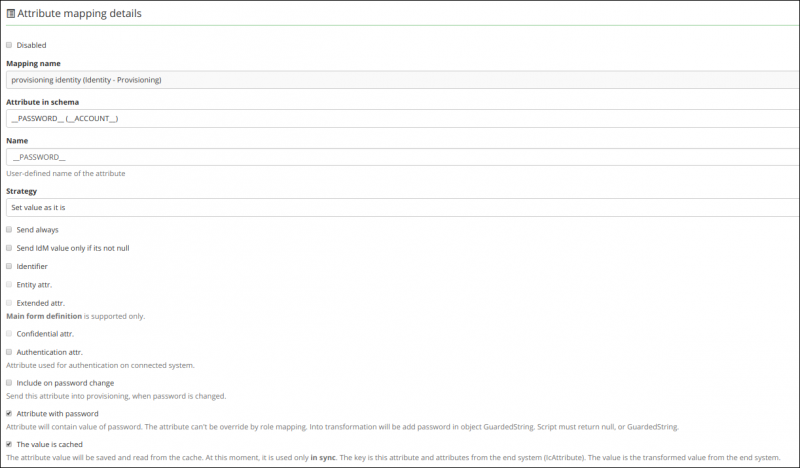
For example: After selecting the password attribute and generating the system schema, it is possible to create a mapping for the password. The main password attribute can be mapped as the __PASSWORD__ attribute.
The main password attribute (__PASSWORD__) is sent to the end system only with the user ID (uid). All attributes, including other attributes marked as password, are sent in separate provisioning operations. If the application property idm.sec.acc.provisioning.sendPasswordAttributesTogether is set to true, only one provisioning operation will be created. This behavior is specific to password changes. When CzechIdM creates a new account on the end system, the password is sent together with other attributes (some connectors may reimplement this behavior, e.g., AD).
All password attributes will be transformed using transformation scripts before provisioning to the end system. The transformation scripts must return a GuardedString or null; any other object will throw an exception. All transformation scripts receive the password in the attributeValue parameter. Classic security rules (e.g., checks for sensitive data) apply to these scripts.
__PASSWORD__.
__PASSWORD__ attribute still exists. For proper functionality, this attribute must have the Password attribute checkbox enabled, otherwise password changes will not work correctly. Existing mappings automatically have this checkbox enabled for all __PASSWORD__ attributes via a flyway script.
Passwords and transformation
Password transformations are applied in these scenarios:
Password change
When a user changes their password for an account (regardless of whether it's their CzechIdM account), the password is first validated against the password policy, then a provisioning operation is triggered for the system using __PASSWORD__. If any transformation script contains errors, it will throw an exception that is not stored in the provisioning operation queue.
Creating a new account and generating a password
When an administrator or automated process assigns a role with a mapped system to a user, and the system's mapping includes password attributes, a new password is generated. This password is transformed by each script in the password attributes. The same password is passed to all scripts.
The password is generated using the password policy configured for the system. If no password policy is defined, the CzechIdM default password policy is used. If even the default policy is missing, no password will be generated. A null value will be passed to the script. Always check for null in the attributeValue parameter in your scripts.
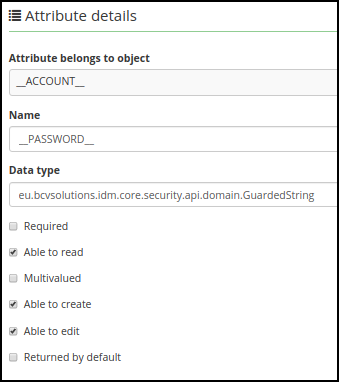
Attribute Password in schema (__PASSWORD__)
__PASSWORD__ attribute is missing, you must create it manually.
- Name:
__PASSWORD__ - Data type:
eu.bcvsolutions.idm.core.security.api.domain.GuardedString - Able to create: true
- Able to edit: true
- Able to read: true
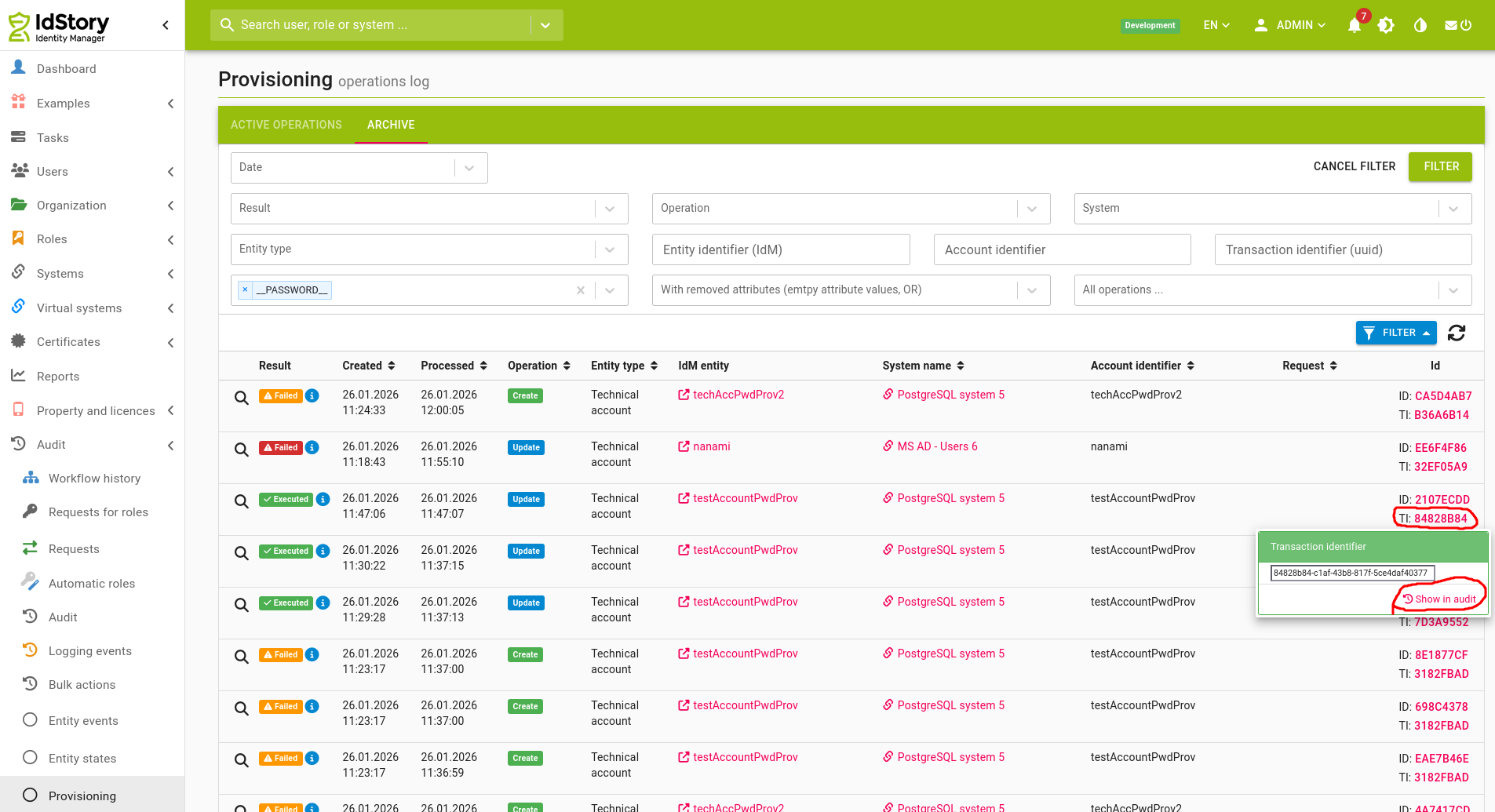
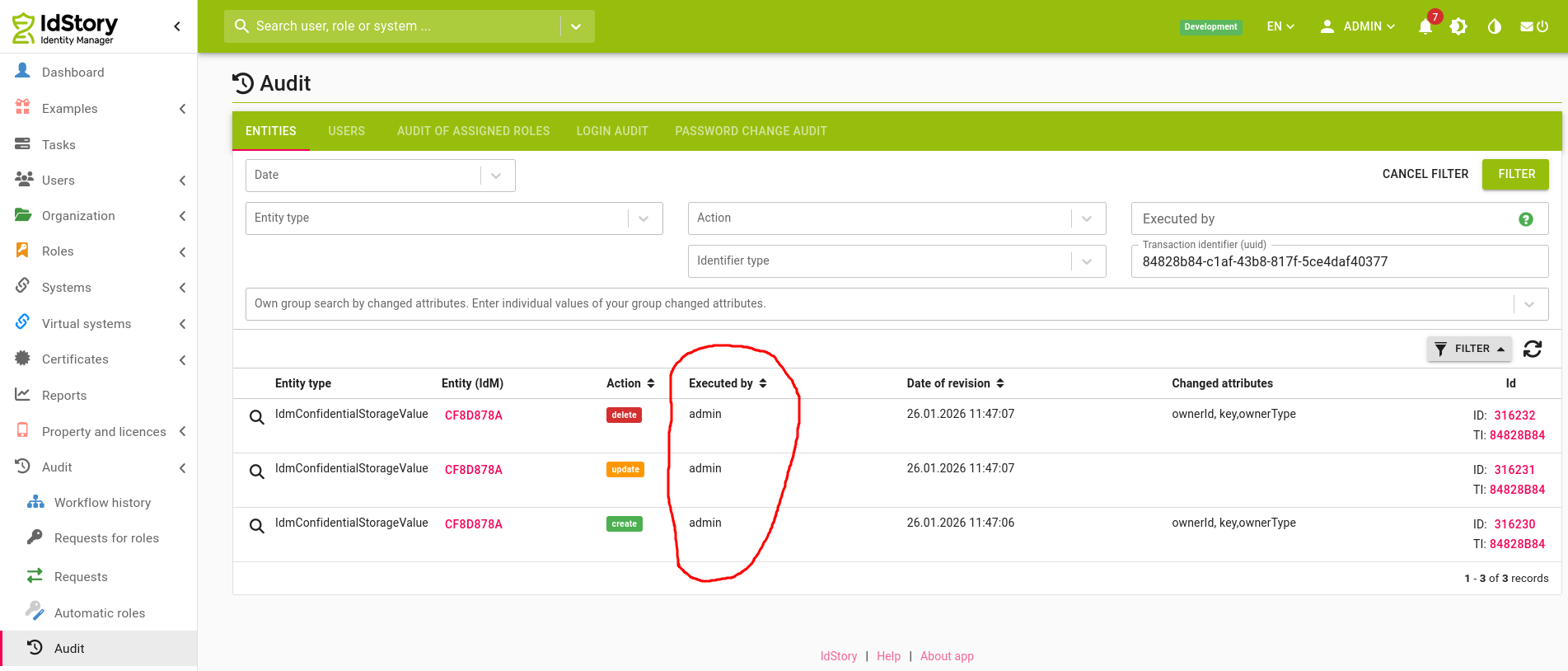
Auditing of password changes
When you want to find who changed the passwords of which accounts, go to the Audit - > Provisioning tab and filter the provisioning records to those that contain the PASSWORD attribute
Then click the T(ransaction) I(dentifier) link and "Show in audit". In the "Executed by" column you'll see who changed the password.